End-to-End WhatsApp: An Opinionated Series on Why Signal Protocol is Well-Designed

WhatsApp recently announced that client communications are now end-to-end encrypted using Open Whisper System’s “Signal Protocol” (previously Axolotl). This has received quite a bit of press lately due to WhatsApp's massive user base, along with the controversial going dark debates. Less importantly, the crypto-nerd in me loves Signal. Because of all of this, I thought I would write a blog series on some of Signal's design decisions that I feel are well-designed.
Secure Password Storage in Go, Python, Ruby, Java, Haskell, and NodeJS

In order to authenticate users, web applications often store user passwords. This can be tricky, because password storage mechanisms are a watering hole for bad advice: there are several solutions to this problem but very few are truly secure. If you store the passwords of your users, your goal should be to make sure that in the event of a data compromise, user passwords should remain safe. The best way to store users passwords is to use a password-based key derivation function (PBKDF) with a sufficient work factor. If your application does not leverage a PBKDF, you should migrate password storage schemes immedietely. More on this later.
Machine Learning Tutorial

We see huge benefits of machine learning in the field of computer security. Much of the work we do on a daily basis can be automated and classified by a machine, leaving us to focus on more interesting and challenging problems. One stunning example is the automated binary exploitation and patching research funded by DARPA for the Cyber Grand Challenge. Problems like these are the stepping stones that will lead us to a future of automated computer security. To encourage future candidates (and ourselves) to delve into the world of machine learning, we built a new technical challenge to test the waters. The challenge is based on a CTF problem from SECCON, discovered by @ctfhacker, and features a mysterious compiler that always produces unique binaries.
IPv6 Has Arrived — Is Your Security Infrastructure Prepared?
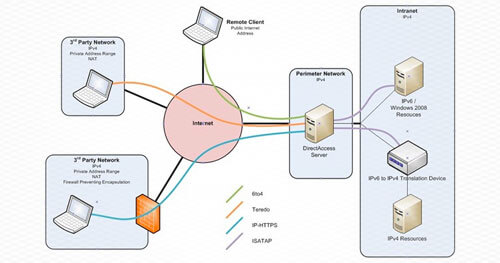
Just over 20 years ago, RFC 1883 – ‘Internet Protocol, Version 6 (IPv6) Specification’ – was published. Since then, exhaustion of the IPv4 address space, and a subsequent migration to IPv6 connectivity has been predicted, heralded, and warned against repeatedly. The seemingly endless stream of warnings and proddings over the past decade to “migrate or else…” have proved unfounded for most organizations. Understandably, this causes many organizations to dismiss or ignore recurring questions about IPv6 adoption, migration, and management plans.
Javascript Sensor API and New Browser Features Raise Privacy Concerns
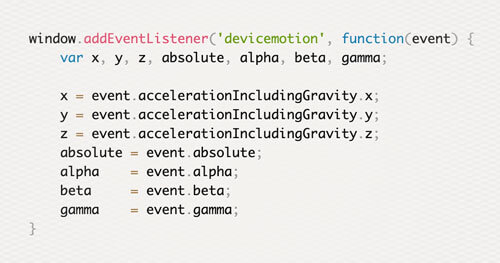
The W3 specs get updated and expand faster than most people can keep up with them. In 2015, many browsers began adding support for mobile sensors which do not prompt users for permission to access them. The new Javascript sensor API and browser features should start raising privacy concerns. These new features allow web applications to be more powerful and ultimately replace the role of many mobile apps. As both a developer and user, it’s important to stay aware of new features and to be mindful of what a website is capable of doing to your mobile device.
Microsoft’s Local Administrator Password Solution (LAPS)

Hackers, incident responders, and penetration testers alike know that valid credential reuse is one of the most common real-world vulnerabilities in today’s networks. Valid credential reuse dominates as the top vulnerability in Verizon’s 2014/2015 Data Breach Investigations Reports Microsoft networks remain amongst the most vulnerable and exploited due to the way in which Active Directory is typically deployed: A base image is created with a standard local administrator password, which is duplicated on all workstations in the environment. When an attacker compromises any workstation, the local administrator password hash can be obtained and used to access every other workstation using the classic Active Directory exploit Pass-the-Hash (PtH). This methodology is described in detail in FireEye/Mandiant M-Trends 2015 case studies.
Statistics Will Crack Your Password
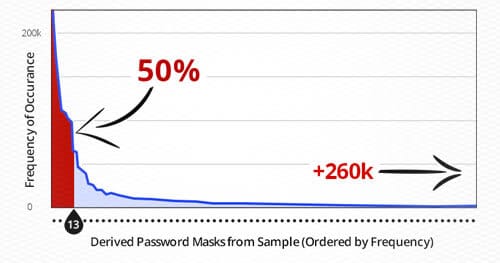
When hackers or penetration testers compromise a system and want access to clear text passwords from a database dump, they must first crack the password hashes that are stored. Many attackers approach this concept headfirst: They try any arbitrary password attack they feel like trying with little reasoning. This discussion will demonstrate some effective methodologies for password cracking and how statistical analysis of passwords can be used in conjunction with tools to create a time boxed approach to efficient and successful cracking.
Navigating Today’s Shared Security Responsibility Model in the Cloud
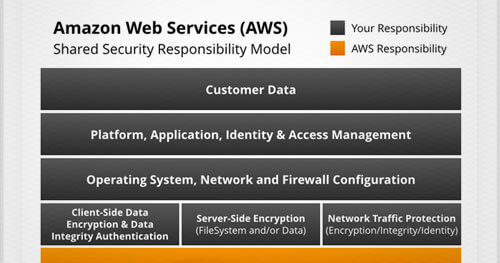
How do you protect the confidentiality, integrity, and availability of systems and data in your organization’s growing cloud environments? It starts by understanding your responsibility.
Addressing security in a public cloud environment is slightly different than in your on-premises data centers. When you move systems and data to the cloud, security responsibilities become shared between your organization and the cloud service provider. Infrastructure as a Service (IaaS) providers, such as Amazon Web Services (AWS), are responsible for securing the underlying infrastructure that supports the cloud, and you are responsible for anything you put on the cloud or connect to the cloud.
NIST Cybersecurity Framework vs. NIST Special Publication 800-53
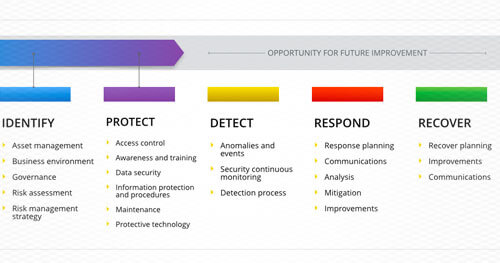
With the recent high-profile attacks on Sony and Anthem, it’s clear that cyber risks continue to grow and that organizations need to do more to strengthen their cybersecurity defenses. Security frameworks exist to guide the implementation and management of security controls, and they should be used by any organization looking to intelligently manage cyber risk. A security framework helps prevent a haphazard approach to information security, and reduces potential gaps in the organization’s security efforts. The ideal framework provides a complete guide to current information security best practices while leaving room for an organization to customize its implementation of controls to its unique needs and risk profile. Several existing and well-known cybersecurity frameworks include COBIT 5, ISO 27000, and NIST 800-53. Recently, a new framework has come into play: NIST’s “Framework for Improving Critical Infrastructure Cybersecurity.”
Cloud Security Best Practices for Amazon Web Services (AWS)

Over the last 18-months we have seen more and more of our clients turn to IaaS (Infrastructure-as-a-Service) providers to support their enterprise infrastructure needs. While there are obvious benefits to utilizing these types of services, such as reducing the complexity associated with managing an enterprise infrastructure, moving to the cloud can also introduce new security concerns. Most often these concerns arise as a result of misconfigured cloud instances.