When HttpOnly Isn’t Enough: Chaining XSS and GhostScript for Full RCE Compromise
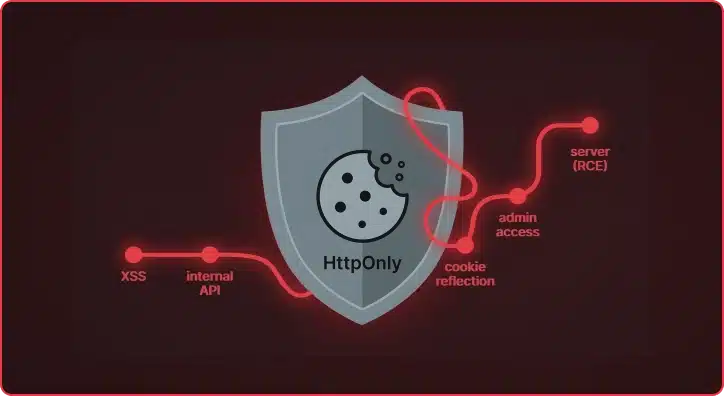
What started as a standard cross-site scripting vulnerability in a document processing platform turned into a full administrative takeover of the application and, ultimately, remote code execution on the underlying server. The HttpOnly flag protected the session cookie from Javascript, but did the application keep it safe? During a recent assessment of a document processing […]
Augustus v0.0.9: Multi-Turn Attacks for LLMs That Fight Back
Single-turn jailbreaks are getting caught. Guardrails have matured. The easy wins — “ignore previous instructions,” base64-encoded payloads, DAN prompts — trigger refusals on most production models within milliseconds. But real attackers don’t give up after one message. They have conversations. Augustus v0.0.9 now ships with a unified engine for LLM multi-turn attacks, with four distinct […]
Et Tu, RDP? Detecting Sticky Keys Backdoors with Brutus and WebAssembly

Everyone knows that one person on the team who’s inexplicably lucky, the one who stumbles upon a random vulnerability seemingly by chance. A few days ago, my coworker Michael Weber was telling me about a friend like this who, on a recent penetration test, pressed the shift key five times at an RDP login screen […]
Mapping the Unknown: Introducing Pius for Organizational Asset Discovery
Asset discovery is an essential part of Praetorian’s service delivery process. When we are engaged to carry out continuous external penetration testing, one key action is to build and maintain a thorough target asset inventory that goes beyond any lists or databases provided by the system owner. Pius is our open-source attack surface mapping tool […]
There’s Always Something: Secrets Detection at Engagement Scale with Titus
TL;DR: Titus is an open source secret scanner from Praetorian that detects and validates leaked credentials across source code, binary files, and HTTP traffic. It ships with 450+ detection rules and runs as a CLI, Go library, Burp Suite extension, or Chrome browser extension — putting secrets detection everywhere you already work during engagements. Say you find […]
Julius Update: From 17 to 33 Probes (and Now Detecting OpenClaw)

TL;DR: Julius v1.2.0 nearly doubles probe coverage from 17 to 33, adding detection for self-hosted inference servers, AI gateways, and RAG/orchestration platforms like Dify, Flowise, and KoboldCpp. The headline addition is OpenClaw, a fast-growing AI agent gateway where exposed instances leak API keys, grant filesystem access, and allow full user impersonation. Update Julius and run […]
As Strong As Your Weakest Parameter: An AI Authorization Bypass
In this AI gold rush, LLMs are becoming increasingly popular with many companies rolling out AI-assisted applications. When evaluating the security posture of these applications, it’s essential to pause and ask ourselves: what are we securing? Automated security tools that test models in isolation play an important role in identifying known vulnerabilities and establishing security […]
Azure RBAC Privilege Escalations: Azure VM

Microsoft Azure provides administrators with controls to limit the actions a principal can take within the cloud environment. These actions can broadly be split into two categories: those that impact the Entra ID tenant and those that affect the Azure cloud subscription, the latter of which we will call “RBAC actions.” Prior research into Entra […]
Leveraging Microsoft Text Services Framework (TSF) for Red Team Operations
The Praetorian Labs team was tasked with identifying novel and previously undocumented persistence mechanisms for use in red team engagements. Our primary focus was on persistence techniques achievable through modifications in HKCU, allowing for stealthy, user-level persistence without requiring administrative privileges. Unfortunately, while we identified an interesting persistence technique, the method we discuss in this […]
Introducing Nosey Parker Explorer

Introducing Nosey Parker Explorer: an interactive review tool for findings from Nosey Parker – the machine learning powered, multi-phase solution for locating secret exposure.