PHP-CGI Remote Command Execution Vulnerability Exploitation

During a recent penetration test, our team found a few web servers that were vulnerable to a PHP-CGI query string parameter vulnerability (CVE-2012-1823). This vulnerability allows an attacker to execute commands without authentication, under the privileges of the web server. The target environment had very strong egress controls in place. All outbound ports were blocked and only ports 80 and 443 were allowed inbound. This made it difficult to obtain an interactive shell. Therefore, we decided to build a proof of concept exploit script using cURL to execute commands and then take it to the next level by authoring a new Metasploit Module.
MAC Cryptographic Errors and Vulnerabilities in SSO Authentication
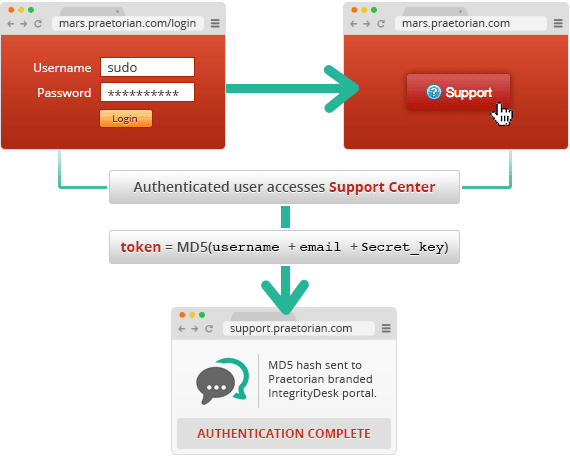
In-house crypto is often a goldmine of cryptographic errors and vulnerabilities. In this post, I’ll describe one of the glaring errors discovered in an online customer support and help desk solution we were considering for use in Praetorian’s cloud-based password cracking service, Project Mars. Hopefully, this can serve as a warning to anyone thinking about writing his or her own crypto libraries.
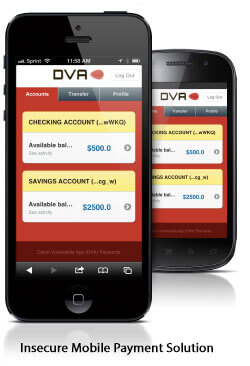
Exploiting Mobile Banking with HeartBleed Vulnerability

For anyone who has not heard, a critical SSL vulnerability called HeartBleed was made public earlier this week that affects a widely used version of OpenSSL. In this post, I will demonstrate the HeartBleed vulnerability being exploited on a vulnerable mobile banking application and backend server within our test environments.
How to Identify and Prevent UIWebView Cross-Site Scripting
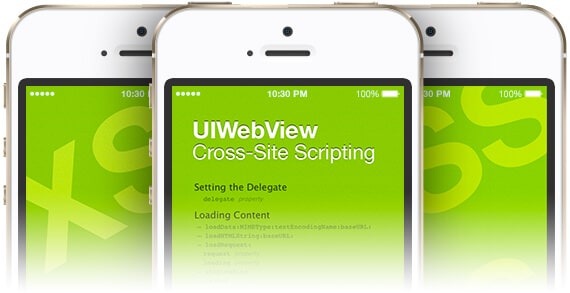
Cross-site scripting occurs when malicious scripts are injected into an otherwise benign or trusted website. Within the mobile security field, cross-site scripting can occur in unlikely places, such as the UIWebView on iOS. For purposes of illustration, we’ll discuss a recent instance of UIWebView cross-site scripting we came across in a test. We’ll also discuss a similar app that does things correctly. Then we’ll cover why problems like this occur and how it’s difficult for developers to foresee these security issues.
How To Identify and Prevent LDAP Injection (Part 2)

LDAP injection occurs when an application fails to neutralize characters that have special meaning in LDAP. Closely, resembling SQL injection, LDAP injection occurs when LDAP statements are constructed with unverified user-supplied data. This can result in the execution of arbitrary commands such as granting permissions to unauthorized queries as well as content alterations within the LDAP tree. The same advanced exploitation techniques leveraged in SQL Injection can be similarly applied in LDAP injection.
How To Identify and Prevent Query and Command Injections (Part 1)

Query and command injections are some of the most devastating classes of vulnerabilities in existence. This series of blog posts will teach you how to identify and prevent this vulnerability from occurring. In part one we will explore examples of command injection.
Develop Secure Mobile Apps by Studying Vulnerable Android, iOS, and Mobile Web Apps
In today’s mobile world, demand for high-quality, feature-rich applications is increasing, while mobile app development cycles are becoming shorter. With time-to-market pressures greater than ever, security vulnerabilities are manifesting themselves in every stage of the mobile app development life cycle. For our summer internship project, we wanted to come up with a way to help developers create more secure mobile apps.
NECCDC Red Team: Quick Twitter Command and Control (C2) Trojan
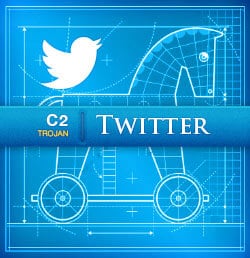
In the last few posts I covered a few C2 Trojans (DNS C2 Trojan, HTTP GET and POST Trojan). In this post I wanted to cover a method that uses Twitter for command and control.
NECCDC Red Team: Quick HTTP Command and Control (C2) Trojans
In my previous blog post, I described the Northeast Cyber Collegiate Defense Competition (NECCDC) and started to explain some of the techniques the red team used. For this post, I’m going to cover two more C2 Trojans that I wrote using HTTP (GET and POST). Similar to the C2 DNS Trojan, the HTTP Trojans are unidirectional and do not require installing software on the victim. By using multiple techniques at varying frequency we increased the likelihood we would be able to maintain persistence throughout the competition.
NECCDC Red Team: Quick DNS Command and Control (C2) Trojan
Recently, I had the opportunity to participate in the Northeast Cyber Collegiate Defense Competition (NECCDC) at the University of Maine. The competition was made up of 10 student groups (blue teams) from various colleges in the region that were tasked with protecting a mock network against a group of professional pentesters (the red team) who were trying to break in. This was my third year on the red team. Prior to the competition, I built several tools that would make life easier for the red team and enable us to differentiate between the qualities of the blue teams we were attacking. I am planning to release the code that I built for the competition over the next few months in a series of blog posts.