Metasploit Integration for Password Auditor
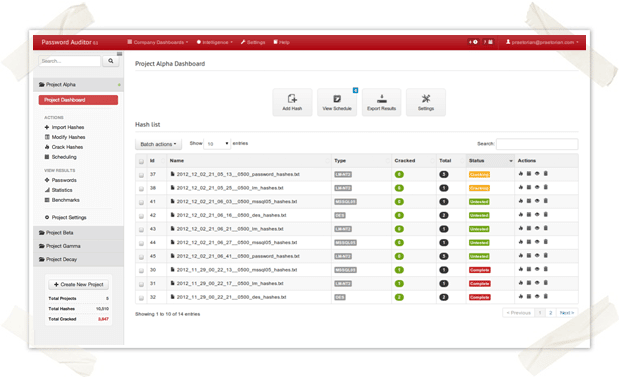
Last week I introduced our new Password Auditor, an internal project I’m working on here at Praetorian. Today, I’m back with a followup screencast that demonstrates one of its major features — Metasploit integration! If you missed the previous screencast, I recommend watching it to get a sense of the tool’s basic functionality.
Password Auditing with Style
In my last post, I announced that our team has been developing an easy-to-use password cracking tool with advanced features. Our initial goal for the project was to create something that made password auditing easier for our services team. However, after several internal discussions we’ve decided to share our work with the security community in order to see if this tool has value beyond what we had initially envisioned. We’ve even talked about opening up a private, invite-only Beta to let others get some hands-on time with the tool. I encourage you to learn more about the tool and leave feedback/comments below (it may increase your chances of receiving an early invitation).
Easy to Use Password Cracking Tool with Advanced Features
Looking back over this past year, I have noticed a continuing theme among public security breaches. Similar to 2011, this year’s high profile security breaches often end in a public dump of confidential victim data. It is not uncommon for Hacktivist groups, such as Anonymous, to publically dump password hashes and other confidential data as a way of proving the breach occurred and as a way of embarrassing the victim.
The Honeynet Project Maps Real-Time Attacks From Around the World
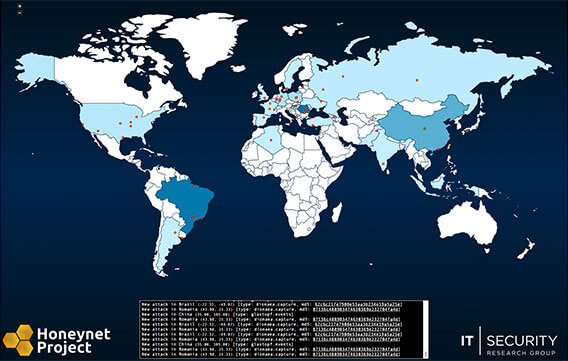
Members of The Honeynet Project’s Giraffe Chapter released a new real-time attack map earlier today. The map shows live attacks from locations around the world, provided by distributed honeypots operated by Honeynet Project chapters. Currently the map is in an alpha release stage, and additional data and input sources are planned for future releases. [Update 9/25/2012: Additional data feeds have been added]
HTTP/HTTPS Bruteforcing Using a List of IPs and Hostnames with Metasploit
Today, I wrote some automation to make it easier to setup and perform HTTP bruteforcing using a list of IPs and hostnames with Metasploit. Metasploit has several auxiliary modules that make it easy to perform various types of bruteforce based attacks. For example, we can easy bruteforce all HTTP BASIC AUTH systems by using the http_login module.
Black Hat USA 2012 (Jabra Edition)

Hey everyone! This week the whole security industry will be in Las Vegas for BlackHat 2012, BSidesLV and Defcon. As I have done for the past few years, I will be teaching Pentesting with Perl at BlackHat. Pentesting with Perl is a course for anyone that has previously coded in nearly any language but wants to learn how to automate some of the common tasks that need to be performed during a pentest. The major change for this year is the course length, which was moved to two days based on feedback from students. The new schedule will make the class much more enjoyable since there will be more time for things like peer-programming, in-depth discussions of materials as well as code walks (by me and the students). People learn best by doing and that is exactly what this class is all about! Again, I’m really looking forward to seeing everyone in Las Vegas this week. I’m always available on Twitter (@Jabra). Feel free to ping me if you would like to meetup. Lastly, if you’re interest in our Puzzles, our next challenge is already underway. Come and find me if you want to try it out firsthand. See you in Vegas! – Jabra